Holiday Shoppers Beware: Domain Spoofing Risks
Vincent D’Angelo, Quinn Taggart and Sue Watts from CSC offer tips for global brand owners and consumers to safeguard against domain security threats.

© AntonioGuillem | istockphoto.com
With the COVID-19 pandemic persisting, online shopping will be the preferred method for the 2020 holiday shopping season. While staying home to shop is the safest option right now, it means consumers are more vulnerable to online fraud, counterfeits, and cyber crime. Increased online activity provides opportunities for unscrupulous infringers to abuse trusted brand names to drive visitors to their own fraudulent content.
Research findings: Holiday shopping and eCommerce domain security briefing
In our latest security briefing, we analyzed the domain security posture of the top 500 global eCommerce and shopping domains*. Then we observed whether these top web properties are being targeted by domain spoofing.
1. Domain spoofing risks
As our recent US election security research showed, domain spoofing is a preferred attack vector. According to the Oregon FBI in their Tech Tuesday, “Cyber actors set up spoofed domains with slightly altered characteristics of legitimate domains. A spoofed domain may feature an alternate spelling of a word (‘electon’ instead of ‘election’), or use ‘[.]com’ in place of ‘[.]gov.’” Additionally, fraudsters are looking to capitalize on consumers restricted to their homes because of COVID-19, especially during the peak holiday shopping season.
To highlight the extent of this threat to brand owners and consumers, we identified and analyzed registered domain typos (misspellings) associated with the top 10 online shopping brands.
Our findings show:
- Over 70% of the 1,553 registered domain typos appear to be owned by third parties. Out of the third-party owned domains:
- Close to 48% are configured with MX (mail) records that can be used to send phishing emails or to intercept email
- 40% are using domain privacy services to mask or hide their ownership and identity showing that they may have some nefarious intentions
Furthermore, these typo domains receive over 5 million visits** annually; a deeper dive of the top 100 most visited typo domains in our research shows they’re being used in this manner:
- 38% are pointing to advertising-related and pay-per-click web content
• Risk: Palo Alto’s recent research showed how pay-per-click domains are used to spread malware via domain parking services. - 27% had no live web content
• Risk: Although these domains do not appear to have web content associated with them, 37% were configured to send and receive email with MX records. - 15% were engaged in affiliate referrals
• Risk: The brand owner could be targeted for unauthorized affiliate activity resulting in financial loss. - 12% were pointing at shopping-related web content
• Risk: The brand owner could experience financial loss and the consumer could be engaging with nefarious retailers selling potential counterfeits and/or receiving a poor shopping experience. - 8% were pointing toward malicious web content
• Risk: The risk is that the consumer could engage with websites that contain malicious content (i.e. malware).
We believe this domain-spoofing problem is vastly underestimated because we know there are hundreds of thousands of registered domains linked to third parties associated with some of these top shopping destinations.
2. Domain security adoption
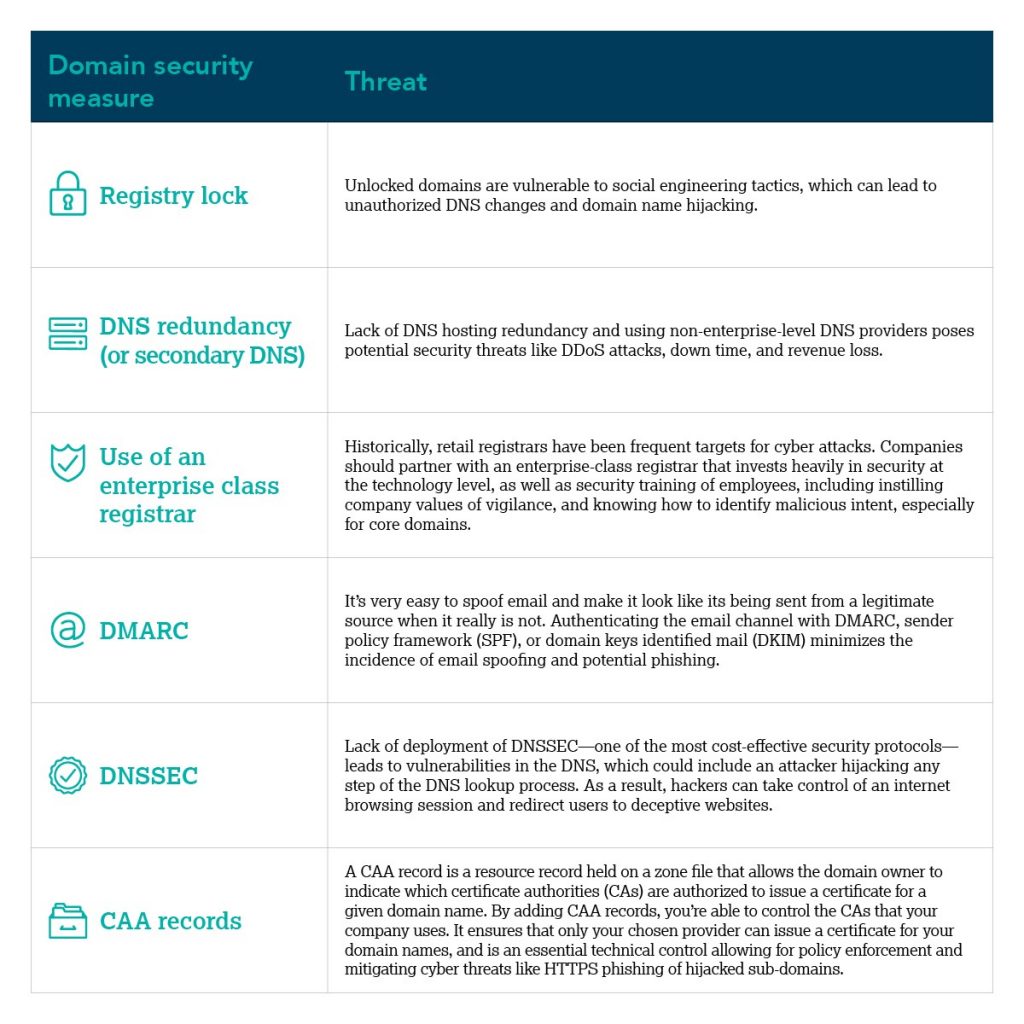
As we observed in our Domain Security Report on the Forbes Global 2000 companies, these eCommerce and shopping web domains fared better than the Global 2000 companies, but still lack basic domain security measures. These businesses are so reliant on online shopping for their revenue that downtime can cost the company $500K+ an hour*.
For example, as noted in a Harvard study on DNS redundancy, it’s surprising that these companies would not secure their online presence from a distributed denial of service (DDoS) attack with only 16% leveraging DNS hosting redundancy. Furthermore, because DNS hijacking could essentially commandeer an organization, we were surprised to see registry lock adoption at only 18%. This is partially explained by the fact that still 40% of the observed domains rely on retail registrars that typically don’t provide advanced domain security features.
Deployment of DNSSEC is close to 3%; DNSSEC is a security measure to prevent DNS cache poisoning. Lastly, although close to 60% of the observed domains had a domain-based message authentication, reporting, and conformance (DMARC) record, we know the lack of a DMARC reject policy still poses phishing risks to hundreds of millions of global consumers.
Below are our findings:

Each of the security measures listed above are industry best practices that help mitigate against cyber attacks, and are a part of CSC’s defense in depth approach.
Three holiday shopping tips for brand owners
- Establish a domain security council that assists with domain strategy and policy. This includes identifying and registering defensive domains in key country markets, including keywords and misspellings. Additionally, the council should champion defense in depth recommendations for secure domain management, including registry lock, reliance on enterprise class domain registrars, DMARC, DNS security extensions (DNSSEC), and DNS redundancy.
- Continuously monitor the domain space and key digital channels like marketplaces, apps, and email for brand abuse, infringements, and fraud.
- Perform global enforcement, including takedowns and advanced techniques in internet blocking.
Four holiday shopping tips for consumers

Below are some additional tips from the FBI***:
- Ensure operating systems and applications are updated to the most current versions.
- Update anti-malware and anti-virus software and conduct regular network scans.
- Use strong two-factor authentication if possible, via biometrics (such as face or fingerprint scans), hardware tokens, or authentication apps.
- Never provide personal information of any sort via email.
- Additionally, in terms of consumer safety online, CSC recommends using the education and awareness materials from the National Cyber Security Alliance (NCSA).
“We’re delighted that companies like CSC are advocating for companies and online brands to put the necessary security protocols in place to protect not only their brand reputation but their consumers, from online fraud and cybercrime,” says Daniel Eliot, Director of Education and Strategic Initiatives at the NCSA. “The National Cyber Security Alliance’s mission is to educate consumers and businesses about these credible risks, and the importance of practicing recommended cybersecurity best practices. CSC’s research is also an important part of advocating for consumers, showing the pervasive risk of these cyber-attacks and fraudulent domains.”
*Data extracted from SimilarWeb.com.
**Approximate estimate based on SimilarWeb’s September’s traffic data, multiplied by 12, to estimated annual visits data.
***fbi.gov/contact-us/field-offices/portland/news/press-releases/oregon-fbi-tech-tuesday-building-a-digital-defense-against-election-spoofing
Please note: The opinions expressed in Industry Insights published by dotmagazine are the author’s own and do not reflect the view of the publisher, eco – Association of the Internet Industry.